5 Tips For Improving The Security Of Your FTP Server
Modern MFT solutions are built with security in mind. If you follow the manufacturer’s installation guide the default settings will give you a secure system. However, enabling some of these extra features can improve the security of your file transfer infrastructure.
Our top recommendations for features you should use if your MFT solution supports them are…
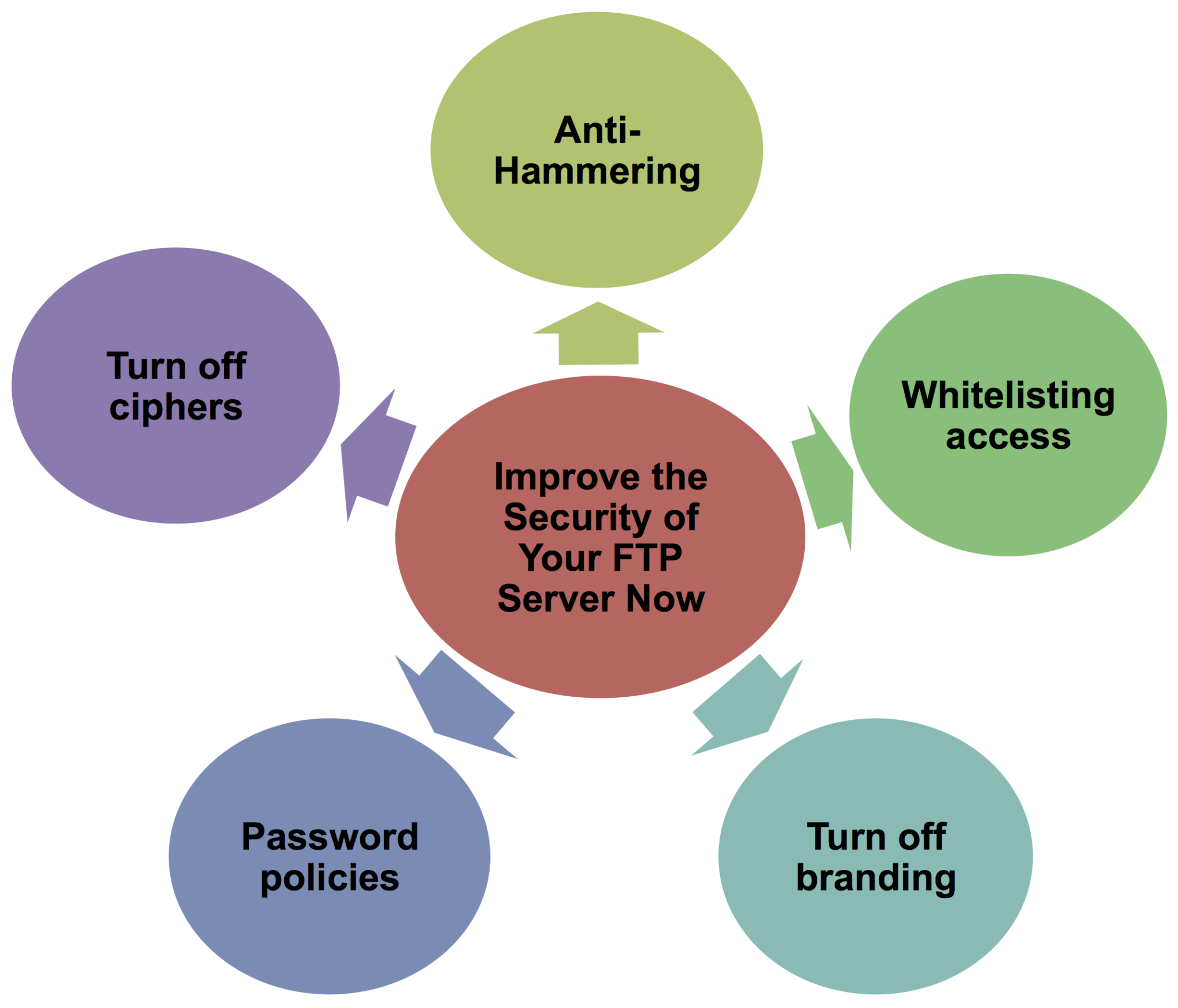
Anti-hammering
Unfortunately, it is not uncommon to be hit by a brute force or DDoS attack on an MFT solution. Good MFT systems can automatically blacklist IP addresses that attempt to brute force their way in. This feature is often turned off by default and as a result , systems can be vulnerable to malicious access attempts. Pro2col recommends enabling this feature, so the MFT system refuses to accept connections either for a set period or permanently from any IP Address which tries to establish too many connections or attempts too many incorrect login attempts within a short period of time.
Whitelisting Access
Moving on from Anti-hammering, the next logical step is to only allow known hosts and IPs to connect to your system. This can either be done on the firewall or by enabling whitelist features in the MFT solution. With Whitelisting turned on, the MFT solution will ignore connection requests from unknown IP addresses. Address ranges can be added for internal users so each internal host does not need to be explicitly defined.
Turn off branding
By default, all MFT solutions have either web interfaces or FTP Connection strings, which publish the name of the product and sometimes even the version number. These can be presented by the system to connections even before a successful login request is made. As a result, any potential attacker could use this information to research known vulnerabilities such as security flaws, which may be patched in more recent versions. Turning these off will not prevent an attacker from working out which MFT product you are using, but it will make it harder and will not advertise any vulnerabilities your software may have until you patch to the latest version.
Password Policies
Strong password policies are turned on by default, but these are often set to a low level of complexity. Often just a six character password requiring numbers and uppercase characters is required. While this is often enough to get started, it would not pass many security audits by organisations or be compliant for standards like PCI-DSS. Pro2col recommend improving the password complexity to at least 8 characters, and adding a “special” character in in addition to the standard security settings. In addition, setting passwords to expire after a period of time and turning on tracking and prevention of re-use of recent passwords will further improve your password security. Many MFT solutions also have a dictionary file, which contains common passwords and can be added to. Checking passwords against this file can also help improve the security of your passwords by removing such well known passwords as “Password” or LetMeIn”.
Further Reading:
Turning off ciphers that are susceptible to attack
Over time Ciphers and MAC algorithms get replaced and improved upon. MFT solutions tend to be set up to allow SFTP connections using any of the known ciphers and macs, even if there are better or more secure versions available. This enables old clients to reliably connect to the system. Turning off ciphers such as twofish-128 and aes-128 will force your SFTP clients to connect using 256bit encryption. This increases security but may also may restrict the ability of older systems or customers with out of date software to connect to your MFT solution.
These features are some of the basics. You may also want to consider housekeeping tasks, encryption at rest and key management.
Further Reading:

Take the risk out of selecting an MFT solution with our free, independent comparison service!
Our comparison report identifies the right solution for your needs and budget. Complete a series of questions and receive a bespoke product recommendation from our technical experts.